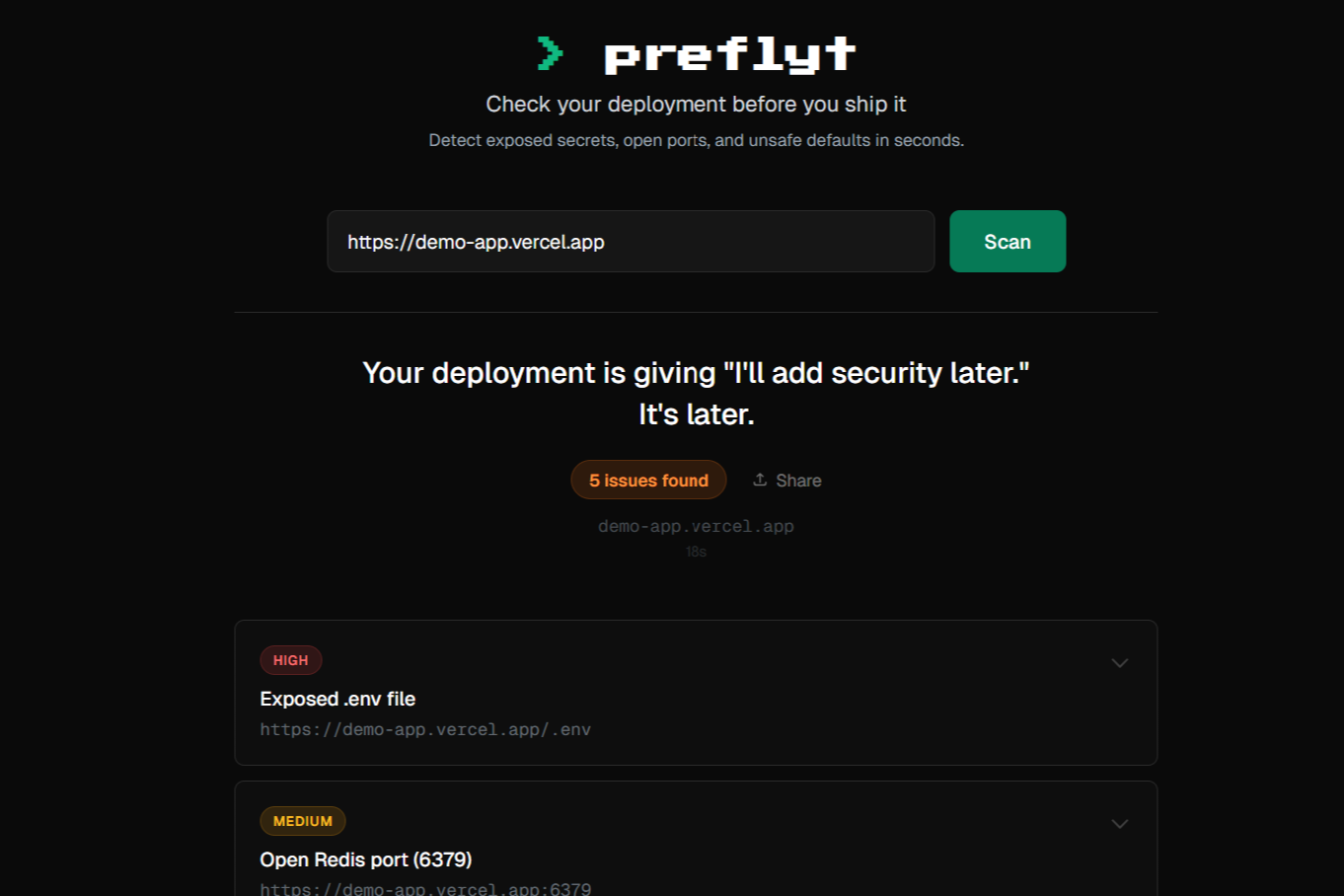
Preflyt
Scan your deployment for security issues in 30 seconds
Preflyt scans your live web app for common deployment security mistakes. Paste a URL or run npx preflyt-check from your terminal - get a report in 30 seconds. Checks for exposed .env files, open database ports, missing security headers, .git directory exposure, and more. No signup required. Works with AI coding agents (Cursor, Claude Code, Copilot) via a skill file that triggers scans automatically after every deploy
Features
- File and Code Exposure Scanning Detects publicly accessible .env files, .git repositories, backup files, source maps, and sensitive configuration files.
- Server and Network Security Scanning Checks for open database ports (MySQL, Postgres, Redis, MongoDB), exposed admin panels, debug endpoints, and dev server ports.
- HTTP Hardening Analysis Verifies security headers (HSTS, CSP, X-Frame-Options), CORS configuration, cookie security flags, and server version leakage.
- Command Checker Paste any terminal command to detect typosquatted packages, hidden unicode characters, and piped downloads before you run them.
Comments

Built Preflyt because I kept seeing the same deployment mistakes everywhere - .env files exposed, database ports open, security headers missing. The code passes all tests but the live deployment is wide open. Preflyt scans from the outside, same perspective an attacker would have. 30 seconds, paste a URL, see what you forgot to lock down
Premium Products
Sponsors
BuyAwards
View allAwards
View allComments

Built Preflyt because I kept seeing the same deployment mistakes everywhere - .env files exposed, database ports open, security headers missing. The code passes all tests but the live deployment is wide open. Preflyt scans from the outside, same perspective an attacker would have. 30 seconds, paste a URL, see what you forgot to lock down
Premium Products
New to Fazier?
Find your next favorite product or submit your own. Made by @FalakDigital.
Copyright ©2025. All Rights Reserved

























